Hackers Use Artificial Intelligence to Compromise Over 600 Corporate Security Systems
By 813 Staff
A major product shift is underway — Hackers Use Artificial Intelligence to Compromise Over 600 Corporate Security Systems, according to The Hacker News (@TheHackersNews) (in the last 24 hours).
Source: https://x.com/TheHackersNews/status/2028841630183403759
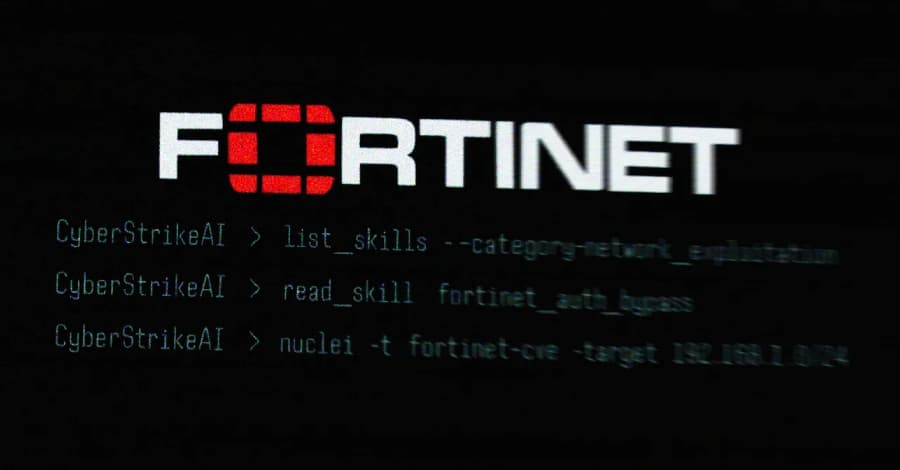
More than 600 FortiGate network security devices have been compromised in what appears to be the first large-scale breach campaign leveraging artificial intelligence tools to accelerate exploitation, according to research published by Team Cymru and reported by The Hacker News on Tuesday.
Internal documents from the investigation show attackers used AI-assisted reconnaissance to identify vulnerable FortiGate firewalls at an unprecedented speed, compressing what would typically take weeks of manual probing into a matter of days. Engineers close to the investigation say the campaign specifically targeted unpatched devices running older firmware versions, exploiting known vulnerabilities that many organizations have been slow to remediate.
The breach affects FortiGate appliances deployed across multiple sectors, though Team Cymru has not yet disclosed which industries or geographic regions saw the heaviest concentration of compromised devices. What makes this campaign particularly concerning to security researchers is the velocity at which attackers moved from initial scanning to full compromise. Traditional attack patterns leave more breadcrumbs and take longer to execute, but the AI-augmented approach allowed threat actors to rapidly pivot between targets and customize their exploitation techniques on the fly.
Fortinet, which manufactures the affected devices, has been dealing with a series of security advisories over the past eighteen months. The rollout of patches has been anything but smooth, with several enterprise customers complaining in private forums about compatibility issues that delayed their update cycles. This created an expanding window of vulnerability that attackers appear to have exploited systematically.
Team Cymru's analysis suggests the campaign began in late February and ramped up significantly in early March, with the bulk of compromises occurring over a concentrated 72-hour period. The security firm used its netflow data and threat intelligence platform to trace the attack infrastructure, though specific attribution details have not been made public.
What remains uncertain is whether the compromised devices have been weaponized for further attacks or if sensitive data was exfiltrated during the breach. Security teams at affected organizations are now conducting forensic reviews, but the investigation is complicated by the fact that many of the compromised devices handle encrypted traffic, making it difficult to reconstruct exactly what the attackers accessed.
Organizations running FortiGate devices should immediately verify they are running the latest firmware versions and conduct thorough security audits. The incident underscores how AI tools are now lowering the technical barrier for large-scale network compromises, a shift that security professionals have been warning about for months but are now witnessing in real time.
Source: https://x.com/TheHackersNews/status/2028841630183403759


