Russian Hackers Hijacked The World's Internet Traffic In Secret Attack
By 813 Staff
Silicon Valley insiders report Russian Hackers Hijacked The World's Internet Traffic In Secret Attack, according to The Hacker News (@TheHackersNews) (in the last 24 hours).
Source: https://x.com/TheHackersNews/status/2041559872140165397
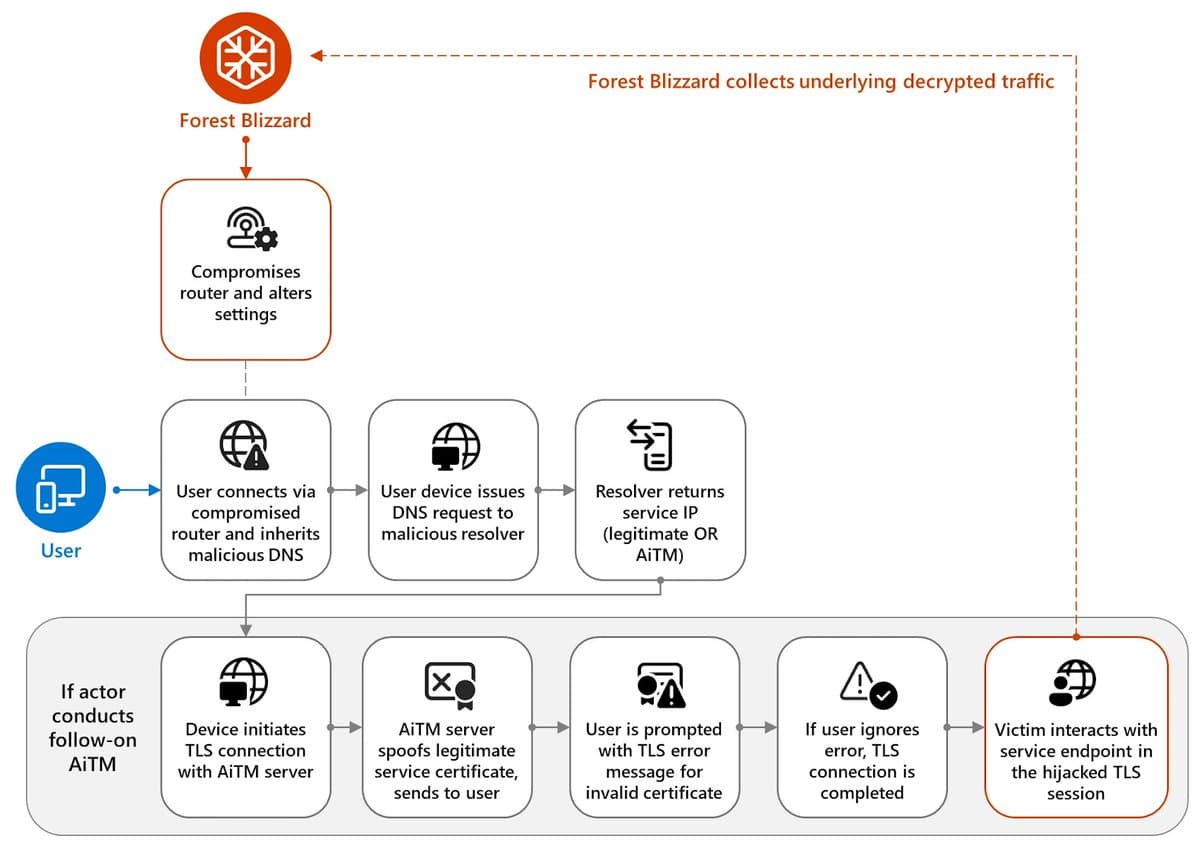
For millions of users who simply turned on their computers this morning, the fundamental trust in their internet connection has been compromised. A sophisticated, state-aligned hacking group has executed a global hijack of commercial and small office routers, creating an invisible surveillance network designed to steal login credentials and private data from unsuspecting victims. The campaign, attributed to the Russian group known as APT28 or Fancy Bear, did not exploit a single new flaw but rather relied on a brutal, simple tactic: using previously leaked default admin passwords to silently seize control of routers worldwide. Once inside, the attackers rerouted the devices’ DNS settings—the internet’s phonebook—to servers they controlled, allowing them to intercept and redirect traffic to fake versions of legitimate websites to harvest credentials.
Internal documents from a coordinated industry response group, viewed by 813, show the scale is immense, targeting devices from multiple manufacturers including Cisco, Netgear, and Asus. Engineers close to the project say the hijack was not limited to any one region but was a globally distributed effort, aiming for breadth over precision to capture as much data as possible. The technical report, first detailed by The Hacker News (@TheHackersNews), indicates the group targeted routers that administrators had never bothered to secure with a unique password, a common issue in smaller businesses and home offices. This operation didn’t just spy on traffic; it actively manipulated it, redirecting users to perfect replicas of email portals, banking sites, and social media login pages to steal usernames and passwords.
The impact here is a stark reminder of the fragility of our network perimeter. While major cloud services and corporate VPNs may have additional protections, the sheer volume of data flowing through a compromised router—from personal emails to business correspondence—is now potentially in the hands of a foreign intelligence apparatus. The consequence is not just individual account theft but the potential for long-term, persistent access to communications and the compromise of entire small business networks. This attack vector, often considered mundane, has been weaponized at an industrial scale.
What happens next is a messy, manual cleanup. There is no single patch to deploy; each compromised device must be reset, have its DNS settings manually verified, and be secured with a new, strong password. The rollout of this remediation has been anything but smooth, as it requires direct action from often non-technical device owners. Internet Service Providers are beginning to send notices, but the onus remains on the user. The uncertainty lies in how much data was already exfiltrated before the campaign was uncovered and how many compromised devices remain under hostile control, continuing to siphon credentials. Security teams are now racing to identify the full list of spoofed domains used in the campaign to add them to blocklists, but for anyone using an older router, a physical reset is today’s urgent task.
Source: https://x.com/TheHackersNews/status/2041559872140165397


