This Secret Cyber War Has Been Hiding In Plain Sight For Years
By 813 Staff
In a move that could reshape the industry, This Secret Cyber War Has Been Hiding In Plain Sight For Years, according to The Hacker News (@TheHackersNews) (in the last 24 hours).
Source: https://x.com/TheHackersNews/status/2032511215831040455
A cybersecurity research group has disclosed a sophisticated, long-running cyber espionage operation focused on military and government organizations across Southeast Asia. The campaign, which has been active for at least three years according to technical evidence, has primarily targeted entities in Vietnam, the Philippines, and Indonesia, with a consistent focus on extracting sensitive defense and strategic information. Internal documents from the investigation, shared with 813 Morning Brief, reveal a methodical approach to intrusion, leveraging custom malware designed to evade standard detection protocols used by national militaries.
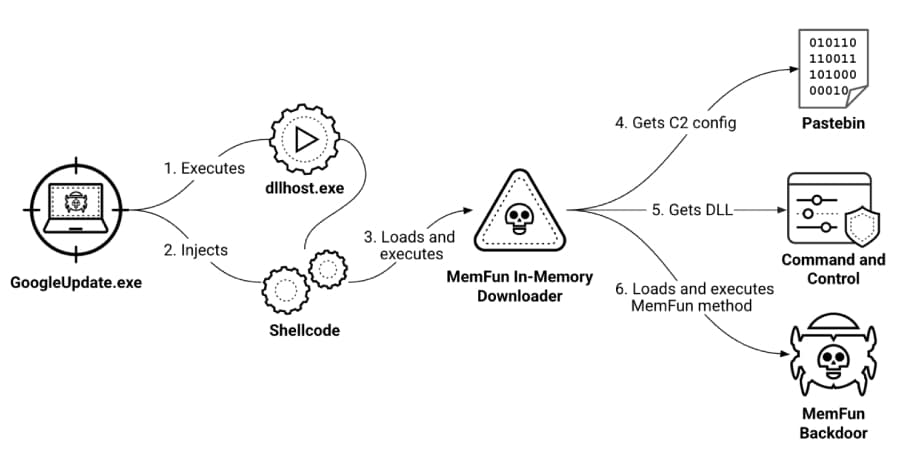
The operation’s infrastructure and attack patterns, detailed in a report by The Hacker News (@TheHackersNews), point to a highly resourced and persistent threat actor, likely state-aligned. Techniques involve spear-phishing campaigns that use convincingly forged documents related to regional security conferences and diplomatic meetings to gain an initial foothold. Once inside a network, the attackers deploy a modular toolkit capable of lateral movement, credential harvesting, and long-term data exfiltration. Engineers close to the project say the code shows signs of continuous development, with updates coinciding with major regional military exercises, suggesting a deep understanding of the operational tempo of its targets.
This matters because it underscores a stark reality in modern geopolitical competition: the front lines are often digital. The compromised data is not merely administrative; it potentially includes communications, deployment plans, and weapons system details. For the affected nations, the breach represents a significant degradation of operational security and a direct challenge to national sovereignty. For technology and defense contractors in the region, it serves as a critical warning about the security of their own systems and the integrity of their data-sharing channels with government partners.
What happens next involves a complex game of attribution and response. While the research has not formally named a responsible state, the targeting pattern and technical signatures will be intensely analyzed by intelligence agencies. The affected governments are now faced with the costly and disruptive process of root-and-branch network cleansing, a rollout that has been anything but smooth in past incidents of this scale. Furthermore, the revelation will likely accelerate existing regional initiatives to develop shared cyber defense protocols, though historical tensions may hinder full cooperation. The campaign’s exposure may temporarily disrupt its activities, but the underlying architecture suggests the actors behind it are prepared for such setbacks and will adapt their methods accordingly.
Source: https://x.com/TheHackersNews/status/2032511215831040455


