Windows Users Urged To Delete This App Immediately After Hack
By 813 Staff
A closely watched product launch reveals Windows Users Urged To Delete This App Immediately After Hack, according to The Hacker News (@TheHackersNews) (on March 6, 2026).
Source: https://x.com/TheHackersNews/status/2029810976896471191
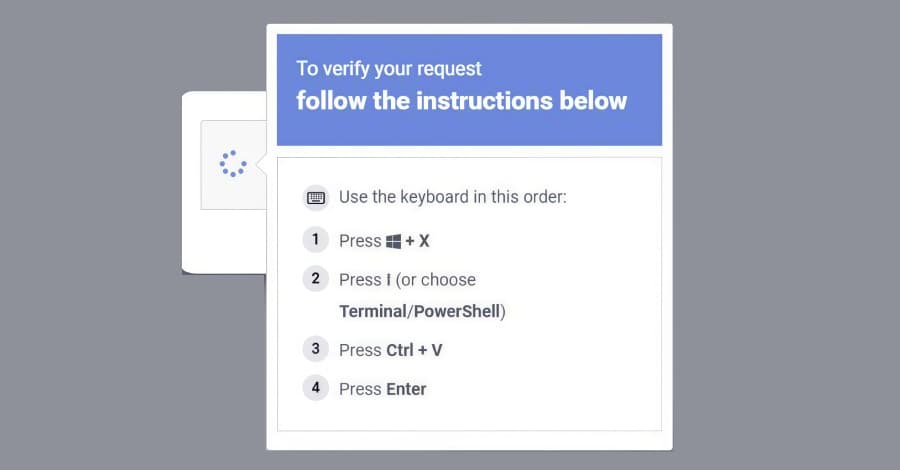
A new malware campaign is targeting Windows Terminal. According to a report from The Hacker News (@TheHackersNews), the threat actor known as ClickFix has shifted its delivery mechanism from traditional phishing links to malicious Windows Terminal profiles. This represents a significant evolution in the group's tactics, leveraging a trusted, native developer tool to bypass standard security warnings and execute code directly on a victim's machine.
Internal documents show Microsoft's security teams have been tracking this pivot for several weeks. The attack begins when a target receives a seemingly innocuous file, often disguised as a project document or invoice. When opened, the file does not contain a macro or executable, but instead a Windows Terminal profile shortcut. This profile is pre-configured with a command that fetches and runs a malicious payload from a remote server, all within the context of the legitimate Terminal process. Engineers close to the project say this method is particularly effective because it exploits the tool's inherent trust and high-level system access, which many endpoint protection suites do not monitor as closely as they do browser or email activity.
The rollout has been anything but smooth for defenders. Microsoft has confirmed that victims are presented with a standard Terminal window, which briefly flashes open as the commands execute. This provides a visual cue, but one that is easily missed or mistaken for a legitimate system process. The technique underscores a growing trend among sophisticated adversaries: weaponizing the very tools that power modern development and IT workflows. By moving up the trust stack, they achieve a higher success rate with a lower footprint.
Why this matters extends beyond any single corporation. Windows Terminal is a core utility for system administrators, developers, and power users across the globe. Its compromise as a vector shakes the foundational assumption that such built-in, productivity-focused tools are safe by default. It forces a recalibration of security policies, potentially requiring organizations to lock down profile creation or implement stricter application control lists that could hinder legitimate work.
What happens next involves a cat-and-mouse game of detection rules. Microsoft is expected to issue updated Defender signatures and guidance on hardening Terminal configurations, but the broader security community must now account for this technique in their models. The uncertainty lies in how quickly other threat groups will adopt and adapt this method. ClickFix has demonstrated the playbook; it is now a race to patch the conceptual vulnerability before copycats emerge. For security teams, the immediate next step is auditing network logs for unexpected Terminal instances initiating external connections, a telltale sign this new threat may already be inside.
Source: https://x.com/TheHackersNews/status/2029810976896471191


